Breaking News
Popular News







Enter your email address below and subscribe to our newsletter
AI News
APIs have become the backbone of the digital economy. In 2026, artificial intelligence systems, cloud services, mobile apps, SaaS platforms, and enterprise tools rely heavily on APIs to exchange data and execute workflows.
But as AI adoption accelerates, APIs are no longer just integration points—they are high-value attack surfaces.
From AI model endpoints to automated agents interacting with multiple services, APIs now power intelligent systems at scale. That makes API security a top priority for organizations building AI-driven applications.
This article explores modern API security risks in the AI era and outlines best practices to protect infrastructure, data, and users.
AI systems amplify API usage in several ways:
Unlike traditional applications, AI-powered systems can generate thousands of API calls in minutes, making misconfigurations or weak authentication mechanisms especially dangerous.


Attackers may exploit unsecured endpoints to:
AI APIs, especially model endpoints, are costly to operate—making abuse financially damaging.
API keys exposed in:
can allow attackers to access AI systems without restriction.
AI systems interacting with external APIs may be vulnerable to prompt injection—where malicious inputs manipulate system behavior or extract sensitive data.
Improperly implemented access control can expose:
APIs that connect AI systems to databases may unintentionally leak sensitive information if access controls are weak.
Use industry standards such as:
Avoid long-lived static API keys whenever possible.
Companies like OpenAI emphasize structured authentication models and key management practices for API usage.
Implement:
Rate limiting prevents both malicious attacks and runaway AI agent loops.
In a Zero Trust model:
Organizations such as Microsoft advocate Zero Trust frameworks for modern cloud and AI infrastructure.
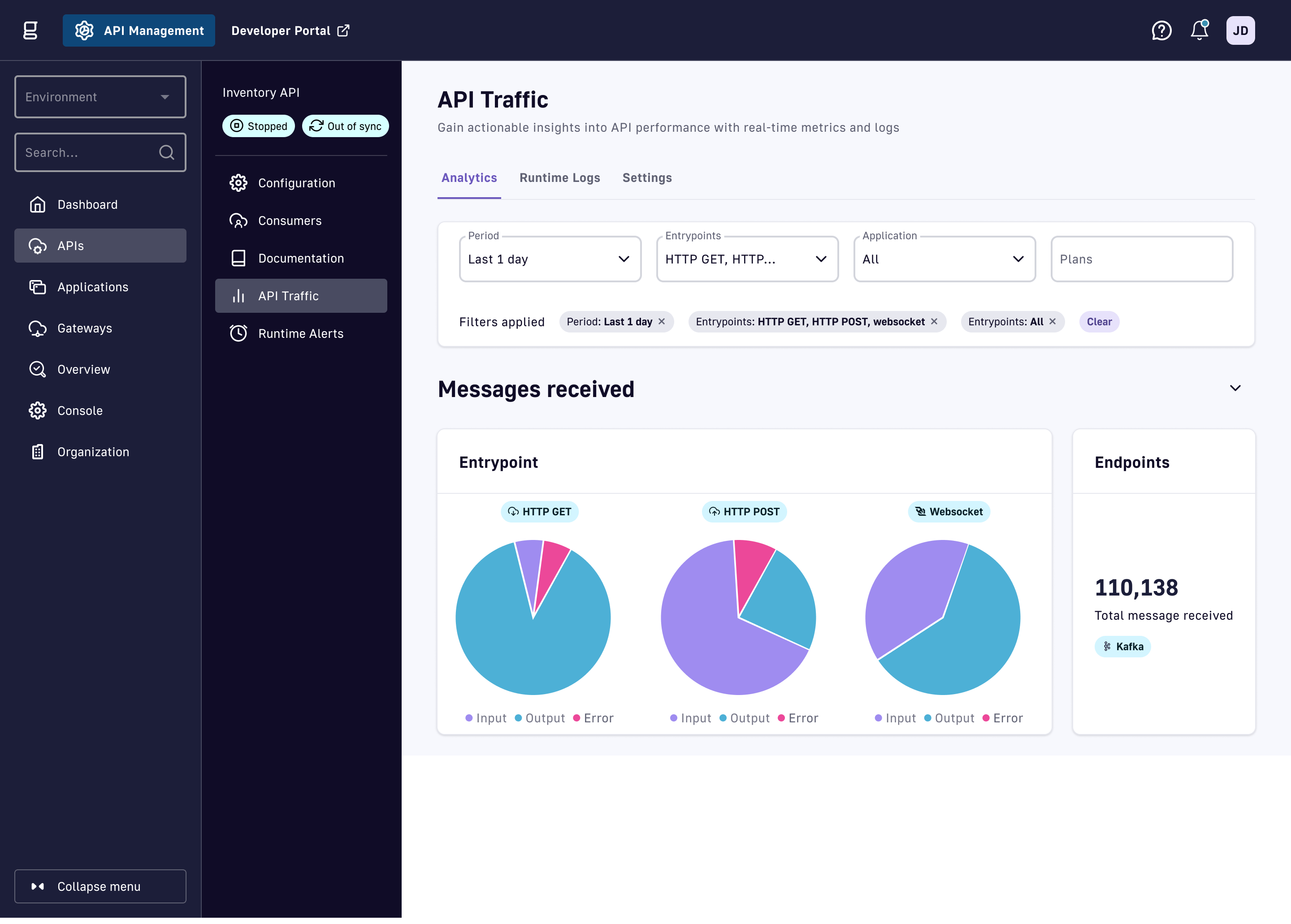
Use API gateways to:
An API gateway acts as a protective shield between external clients and backend services.
Ensure:
Encryption prevents interception of sensitive API communications.
AI-powered APIs require additional safeguards:
AI systems interacting with tools or databases must isolate execution environments to prevent lateral movement.

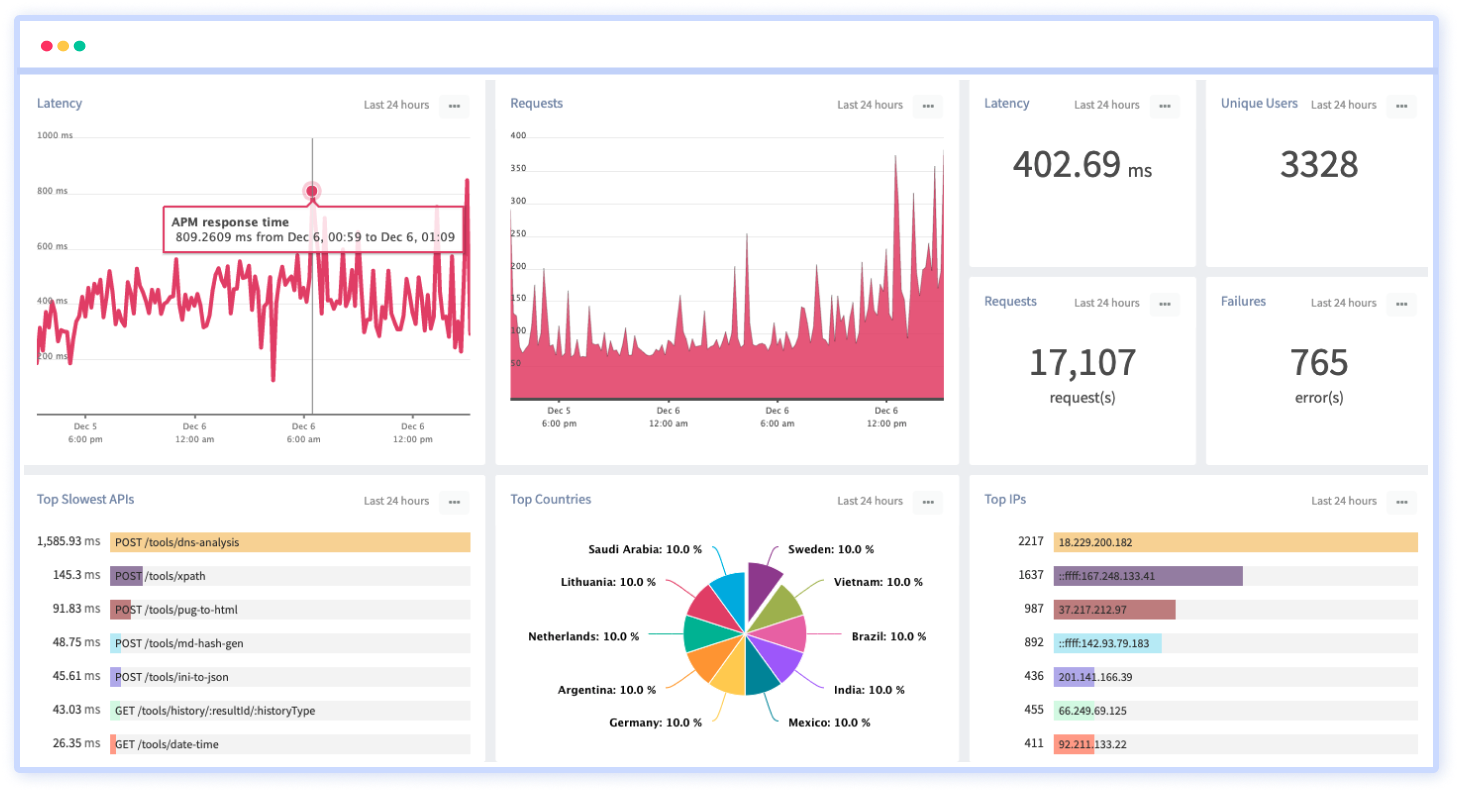

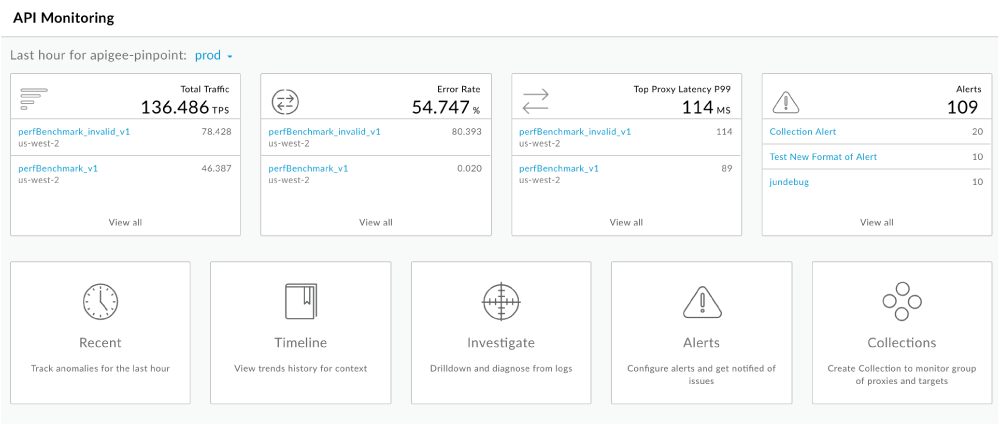
Modern API security requires:
AI can also enhance security by detecting unusual patterns faster than rule-based systems.
Never hard-code credentials.
Instead, use:
This prevents accidental exposure of API keys and tokens.
Conduct:
AI APIs evolve rapidly—security practices must evolve alongside them.
In 2026, AI agents often interact autonomously with APIs.
To secure agent-based systems:
Autonomous systems should never have unrestricted production-level privileges.
API security now intersects with:
Organizations must ensure API data flows align with regional regulatory requirements.
APIs power the AI ecosystem. As AI systems grow more autonomous and interconnected, API security becomes mission-critical.
The age of AI requires more than basic authentication—it demands layered defenses, Zero Trust principles, real-time monitoring, and AI-aware threat modeling.
Organizations that prioritize API security will not only reduce risk but also build trust in their AI-powered platforms.
In 2026, secure APIs are not optional—they are foundational to responsible AI deployment.